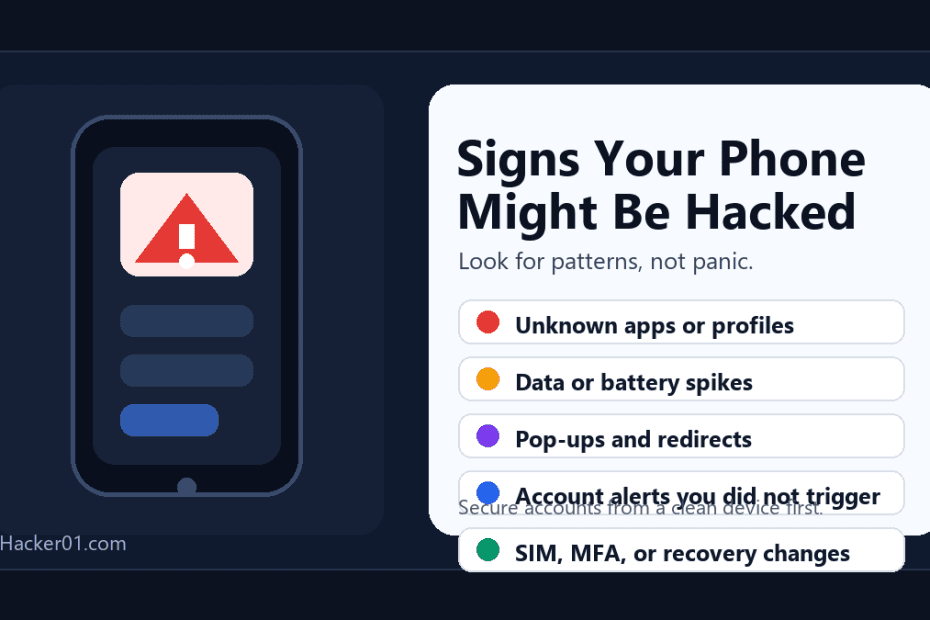
If you are searching for signs your phone is hacked, start with patterns instead of panic. A hot phone, weak battery, or slow app does not automatically mean someone has compromised your device. But when those symptoms appear together with unknown apps, strange account alerts, pop-ups, messages you did not send, or changes to recovery settings, you should treat the situation seriously.
The strongest warning signs are unfamiliar apps or profiles, aggressive browser redirects, unusual data usage, security alerts you did not trigger, outgoing texts or calls you do not recognize, and account recovery changes you did not make.
Quick checklist: signs your phone may be hacked
- Unknown apps, VPNs, profiles, or permissions appear.
- Your mobile data or battery usage suddenly spikes.
- Pop-ups, fake virus warnings, or browser redirects keep returning.
- Texts, calls, emails, or social messages are sent without you.
- You receive MFA codes, password reset emails, or login alerts you did not request.
- Recovery email, phone number, passkeys, or trusted devices change.
- Your phone gets hot or drains battery while idle.
- Security tools warn about unsafe software or stop working.
- Your SIM, phone number, call forwarding, or text delivery changes unexpectedly.
- The phone becomes unstable after installing a risky app or sideloaded file.
Not every phone problem is a hack
Before you assume the worst, separate normal phone problems from real compromise signals. Battery drain can follow a major operating system update. Overheating can happen during charging, gaming, navigation, or video calls. Slow performance can come from low storage or an aging device.
The situation becomes more serious when ordinary device symptoms appear alongside account-security clues. Password reset prompts, MFA codes you did not request, unfamiliar trusted devices, new forwarding rules, or changed recovery details are much harder to explain away.
| Weak signal on its own | Stronger warning sign |
|---|---|
| Battery drains faster after an update | Battery drains while the phone is idle and unknown apps appear |
| Phone gets warm during charging or video calls | Phone gets hot while unused and data usage also spikes |
| One app crashes after an update | Security tools stop working or warn about unsafe software |
| You forgot a password | You see login alerts, recovery changes, or MFA codes you did not request |
1. Your battery suddenly drains much faster than normal
Battery drain is one of the most common warning signs, but it is also easy to misread. Malware, spyware, hidden background syncing, or abusive apps can consume power. So can poor signal, an old battery, or a recent OS update.
It becomes suspicious when the drain starts after installing an unfamiliar app, the phone gets warm while idle, data use climbs at the same time, or battery health was stable before the change.
2. Mobile data usage spikes for no clear reason
Spyware, adware, and account-takeover tools often need to communicate with outside servers. That can show up as unusual background data use.
Check for a sudden jump in cellular usage, apps consuming data that you barely use, background data from an app you do not recognize, or heavy data activity while the phone is idle. Android users should review Google Play Protect and recently installed apps if the change started after a new install.
3. You find apps, profiles, or permissions you did not set
This is one of the strongest red flags. Look for an app you do not remember installing, a device-management profile you did not approve, accessibility permissions enabled for an app that should not need them, a VPN or keyboard you did not set up, or apps asking for SMS, microphone, camera, location, or notification access without a good reason. For business or app owners, this is also where a formal mobile app security audit scope can help separate device issues from application risk.
On Android, remove apps you do not trust and review Play Protect. On iPhone, check app permissions and look for unknown profiles under VPN & Device Management if that option appears.
4. Pop-ups, browser redirects, or fake virus warnings keep appearing
If your browser opens unfamiliar pages, your homepage changes on its own, or you keep seeing fake warnings that your phone is infected, you may be dealing with adware, a malicious site permission, or unsafe software.
Do not trust the pop-up itself. Exit the page, clear the browser data if needed, review site notification permissions, and check recently installed apps.
5. The phone gets unusually hot while you are barely using it
A phone that heats up during charging or heavy use is not unusual. A phone that runs hot while sitting still can be. This matters more when it happens with fast battery loss, constant background activity, unexpected camera or microphone indicators, or strange permissions tied to a recently installed app. If the concern is an iPhone tied to important data, see our related guide on iPhone security and data retrieval help.
6. Strange texts, calls, or messages go out from your number
If contacts say they received odd texts, links, or calls from you, your phone number, messaging app, or linked accounts may already be abused. Watch for SMS messages you did not send, WhatsApp or social DMs you do not recognize, outgoing calls that are not yours, and MFA codes arriving because someone is trying to break into your accounts.
7. You get locked out of accounts or see security alerts you did not trigger
In practice, the clearest evidence of compromise often appears in your accounts before it appears on the device. Apple lists warning signs such as account activity you do not recognize, MFA codes you did not request, unknown trusted devices, purchases you did not make, and password changes you did not initiate. Google also recommends checking recent security events and unfamiliar devices if you suspect account compromise.
Check immediately for password reset emails or texts you did not request, recovery email or phone changes, new trusted devices, sign-ins from unfamiliar places, and banking or payment alerts that do not make sense.
8. Your security tools stop working or your phone warns you about unsafe software
If an antivirus app suddenly stops running, Play Protect warns about a harmful app, or your iPhone blocks an app because it contains malware, do not brush it off. A security warning on the device is one of the most actionable signals you can get.
9. Your number, SIM, or forwarding behavior changes unexpectedly
Sometimes the attacker is not inside the phone at all. They may be targeting the phone number tied to your accounts. Pay attention if calls suddenly stop reaching you, text-based MFA codes stop arriving, your carrier shows forwarding changes you did not set, or you lose service after strange account activity.
If this happens, contact your mobile carrier from a trusted device and ask them to confirm SIM status, number porting, account changes, and call or SMS forwarding settings.
10. Storage disappears, apps crash, or the phone becomes unstable after a risky install
A major drop in device speed, unexpected storage loss, or a phone that stops working properly can be a malware symptom. It is more urgent if the instability starts after a sideloaded APK, sketchy browser prompt, unofficial app-store install, or fake cleanup app.
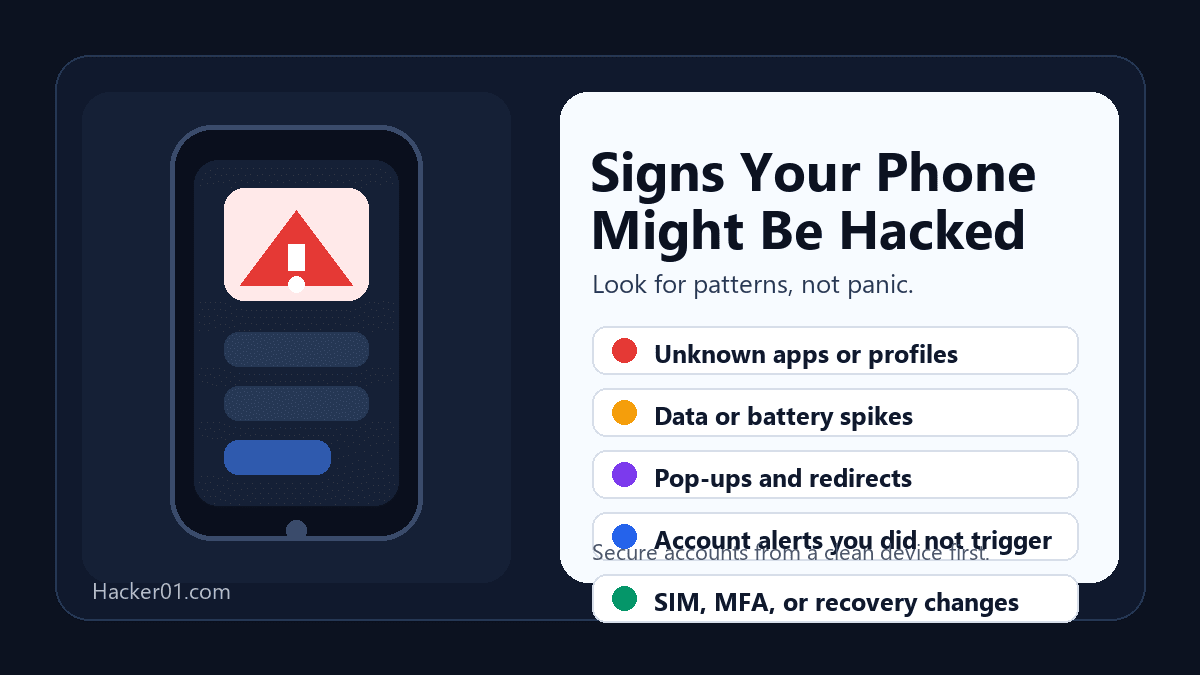
What to do in the first hour
1. Stop using the phone for sensitive activity
Do not keep logging into email, banking, crypto, password managers, or admin accounts on a device you no longer trust.
2. Secure your most important accounts from a clean device
Use a laptop or another trusted phone to change passwords for your main email, Apple Account or Google Account, banking apps, social accounts, and password manager. Turn on MFA if it is not already enabled.
3. Review connected devices and recovery settings
Check for unfamiliar devices, backup emails, recovery phone numbers, passkeys, app passwords, and forwarding rules.
4. Remove suspicious apps and review built-in protections
For Android, open Google Play Store, review Play Protect, remove apps you do not trust, and install available Android security and Google Play system updates.
For iPhone, delete apps that triggered malware alerts, review permissions under Privacy & Security, check for unknown profiles under VPN & Device Management if present, and use Safety Check if you are concerned about broader sharing access.
5. Back up what you need, then update or reset if necessary
If suspicious behavior continues after removing risky apps and securing accounts, a factory reset may be the safest path. Back up necessary files first, but avoid blindly restoring a backup that could reintroduce the same app, profile, or setting.
6. Contact your carrier or bank if money or MFA is involved
If your number, SIM, text messages, or transaction history looks wrong, contact the carrier and bank immediately. A device cleanup will not fix a SIM-swap, account takeover, or active fraud issue by itself.
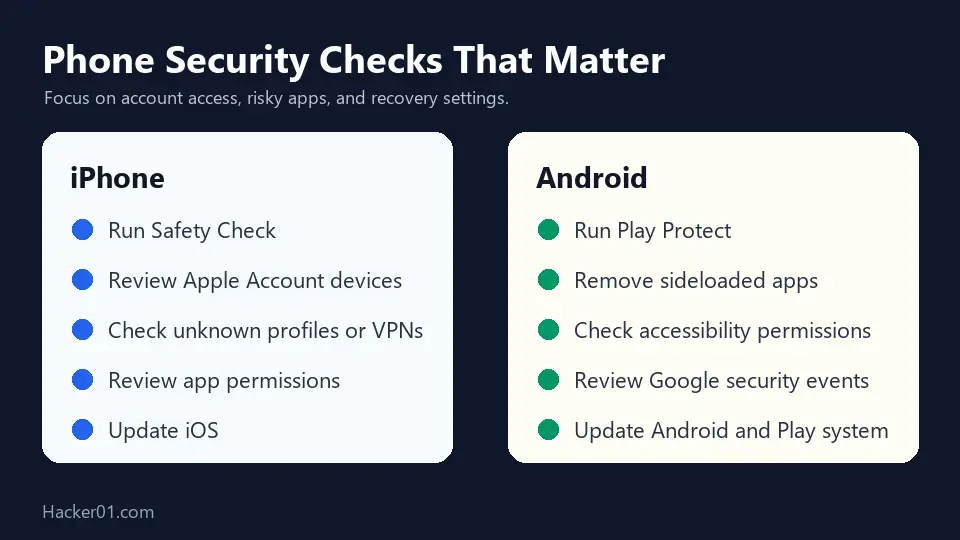
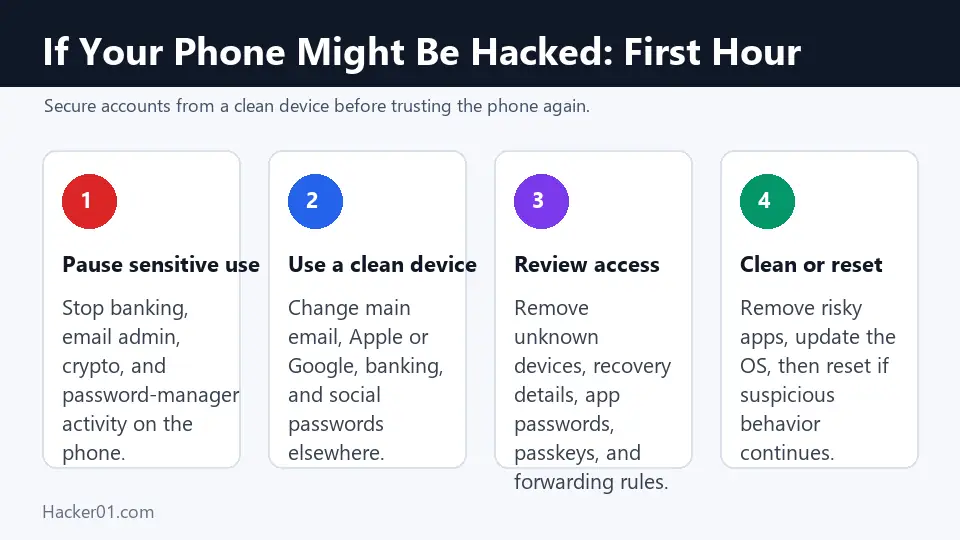
iPhone checks that matter most
If you use an iPhone, the highest-value checks are usually account and sharing reviews, not random secret codes. Start with:
- Apple Safety Check
- Apple guidance for a compromised Apple Account
- Apple password security recommendations
Android checks that matter most
Android users should be especially cautious about sideloaded apps, fake browser prompts, and apps with excessive permissions. Start with:
- Google Play Protect
- Google: remove malware or unsafe software on Android
- Google Account security review
If you think this is stalkerware, act carefully
Hidden phone-monitoring tools can be part of abuse situations. The FTC warns that taking action from the same phone may alert the person monitoring you. If your concern involves a partner, ex, employer, or anyone who may have physical access to your device, use a safer device when possible and review the FTC guidance on stalkerware.
When to get outside help
Most people should start with the official Apple, Google, carrier, bank, or platform recovery routes first. Outside help makes more sense when the phone is tied to a business, legal, or fraud matter, recovery settings were already changed, you need evidence preserved, or several accounts were exposed through the same device. Before hiring anyone, review our legal guide to ethical cybersecurity help.
For related recovery guidance, read how to get a hacked account back and our guide to safe account recovery help or 5 signs your account is hacked and the recovery steps that work. If the situation is authorized and urgent, you can also contact the team.
FAQ
Can a phone be hacked without obvious symptoms?
Yes. Some compromises stay quiet at first. That is why account-level clues like unknown devices, recovery-setting changes, and unexpected MFA codes matter as much as battery drain or pop-ups.
Does overheating always mean my phone is hacked?
No. Heat is a weak signal on its own. It matters more when it appears with strange apps, aggressive data use, security alerts, or suspicious account activity.
Should I factory reset my phone immediately?
Not always. First secure your key accounts from a clean device, document suspicious activity, remove risky apps, and review built-in protections. If the device still behaves suspiciously or you cannot trust it, a reset may be the safest next move.
What is the fastest way to check if someone got into my accounts through my phone?
Review your Apple Account or Google Account security page, check recent security events, look for unfamiliar devices, confirm recovery settings, and change important passwords from a trusted device.
Final word
The best way to think about this topic is not “What one symptom proves a hack?†It is “What combination of symptoms tells me I need to act now?†Focus on the signs that are hardest to explain away: unfamiliar apps, account alerts, changed recovery settings, messages sent without you, and security warnings from the phone itself.
Last reviewed: April 2026. This guide was refreshed using current Apple, Google, and FTC guidance so the advice reflects current iPhone and Android security workflows.