In today’s digital age, privacy is a major concern. One common worry is whether someone can read your text messages from their phone. This article explores how such a scenario could occur, signs your messages might be compromised, and steps to protect your privacy.
Table of Contents
ToggleCan Someone Read My Text Messages? Privacy Risks Explained
Is It Possible for Someone to Read Your Texts from Their Phone?
Yes, it’s possible, but it usually requires specific conditions, such as:
- Unauthorized Access to Your Device:
- Someone with physical access to your phone can install spyware or malicious apps.
- Syncing your phone to their device via cloud services (e.g., iCloud, Google account) can give them access.
- Spyware or Monitoring Apps:
- Apps like mSpy or FlexiSPY, when installed, can log your messages and send them to another device.
- These apps often require brief physical access to your phone.
- SIM Card Cloning:
- By cloning your SIM card, hackers can intercept messages sent to your phone number.
- This is a highly technical and less common method.
- Social Engineering or Phishing:
- Attackers trick you into revealing login credentials for your accounts, gaining access to synced messages.
Signs Someone Might Be Reading Your Messages
- Unusual Activity on Your Phone:
- Unexpected battery drain or overheating.
- Messages marked as read when you haven’t viewed them.
- Login Notifications:
- Alerts from apps or services about logins from unknown devices.
- Receiving Fake Texts or Links:
- Phishing attempts often involve fake texts to gather more personal information.
How to Protect Your Text Messages
1. Secure Your Phone
- Use a strong passcode or biometric authentication (e.g., fingerprint or facial recognition).
- Avoid sharing your phone or leaving it unattended.
2. Enable Two-Factor Authentication (2FA)
- Use 2FA for your cloud accounts to prevent unauthorized syncing.
- Apps like Google Authenticator or built-in 2FA settings add an extra layer of security.
3. Check for Spyware
- Use trusted antivirus or anti-spyware apps to scan your phone. Examples include Avast, McAfee, or Malwarebytes.
- Factory reset your device if you suspect spyware (back up your data first).
4. Avoid Clicking Suspicious Links
- Don’t click on unknown links in texts or emails, as they might lead to phishing or malware.
5. Review App Permissions
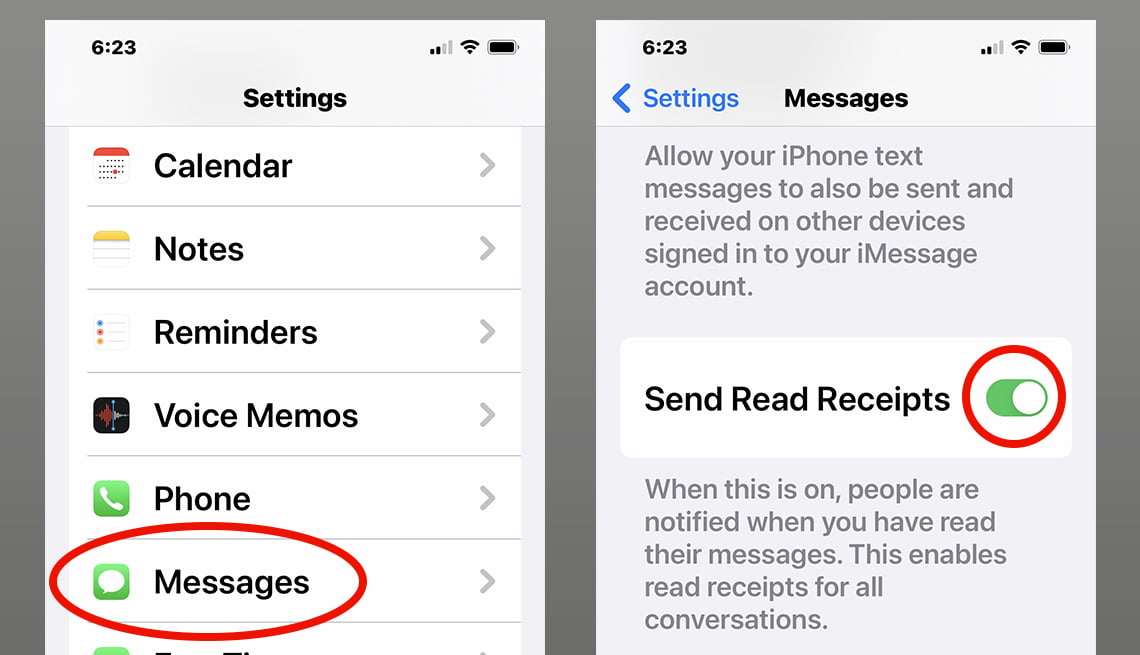
- Go to your phone’s settings and check app permissions for access to messages or data.
- Revoke unnecessary permissions.
6. Monitor Your Accounts
- Regularly check for unauthorized devices or sessions in your cloud accounts (e.g., Google, Apple ID).
7. Update Your Software
- Keep your phone’s operating system and apps up to date to patch vulnerabilities.
What to Do If You Suspect Your Messages Are Compromised
- Change Passwords: Update passwords for your accounts immediately.
- Log Out of All Devices: Use the “log out of all devices” feature available in most apps.
- Contact Your Carrier: Inform them if you suspect SIM cloning or other compromises.
- Reset Your Phone: Perform a factory reset to remove any hidden spyware or malicious apps.
Conclusion
While it’s possible for someone to read your text messages from their phone, taking proactive security measures can significantly reduce the risk. Stay vigilant, use strong passwords, and regularly monitor your accounts for unusual activity to protect your privacy.